The digital threat landscape has undergone a radical transformation as modern cyber adversaries transition from prolonged, exhausting sieges to lightning-fast, high-capacity strikes that can paralyze a network in seconds. Recent data indicates that while the raw frequency of Distributed Denial of Service events has stabilized at a historically high level, the structural nature of these incidents has shifted toward extreme brevity and massive bandwidth consumption. This evolution is driven primarily by the maturation of the Internet of Things ecosystem and the integration of sophisticated automation tools that allow attackers to mobilize massive botnets with surgical precision. Unlike the multi-day disruptions of the past, contemporary incursions are often measured in minutes rather than hours, reflecting a tactical pivot intended to overwhelm automated mitigation systems before they can effectively pivot or scale their response. As these rapid-fire bursts become the standard operating procedure for threat actors, the window for human intervention has essentially closed, forcing a fundamental reassessment of how organizations safeguard their digital infrastructure from sudden, catastrophic surges in malicious traffic.
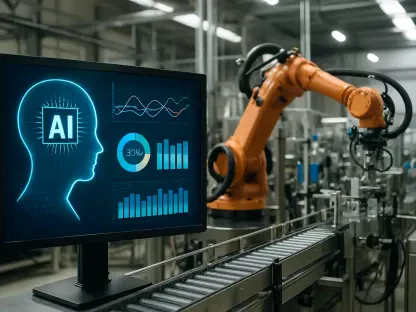
This metamorphosis in attack methodology is deeply rooted in the accessibility of professional-grade stresser services and the democratization of artificial intelligence for offensive operations. In 2026, the barriers to entry for launching a high-capacity strike have vanished, enabling even low-skill actors to rent substantial computing power for short, targeted windows. Building on this foundation, the average magnitude of these incidents has ballooned by approximately 70% within the current year, even as the duration of the vast majority of attacks has dropped below the ten-minute mark. These tactical strikes are specifically engineered to bypass traditional threshold-based detection, which often relies on sampling or historical averages to identify anomalies. By the time a legacy scrubbing service identifies the surge and begins rerouting traffic, the damage is already done, and the attacker has already vanished. This trend highlights a move toward quality over quantity, where the objective is not just to occupy bandwidth but to trigger specific failure points in stateful firewalls, load balancers, and application delivery controllers through sheer, concentrated intensity.
Tactical Shifts and Industry Vulnerabilities: The Rise of Industrial Targeting
The geographic and sectoral focus of these digital assaults has moved away from traditional telecommunications backbones toward specific end-user environments that offer higher operational leverage. Historically, hackers sought to disable regional providers to maximize the scope of the outage, yet the share of attacks directed at telecom entities fell from 42% last year to just 24% in 2026. This trend suggests that adversaries are increasingly interested in the immediate financial and operational fallout of targeting private enterprises and public institutions directly. Education and the public sector have seen a notable uptick in activity, but manufacturing has emerged as the most vulnerable frontier. Modern industrial facilities rely heavily on interconnected automation and real-time sensor data, making them particularly susceptible to even brief interruptions. An 11.6 Gbps burst—now considered a standard average for the sector—is more than sufficient to desynchronize automated production lines, leading to equipment damage, lost revenue, and significant safety risks. This shift demonstrates that the perceived value of downtime has become a primary driver for choosing targets in the current environment.
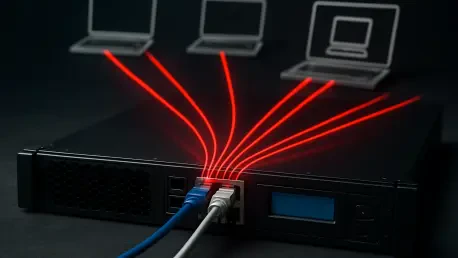
As organizations look toward 2027 and beyond, the necessity of transitioning from reactive cleanup to proactive, always-on mitigation has become undeniable. Traditional on-demand protection models, which require a manual or semi-automated redirect to a scrubbing center, are no longer sufficient against attacks that conclude before the redirection is complete. This approach naturally leads to the implementation of edge-based security architectures that utilize local processing and global threat intelligence to filter traffic in real-time. Organizations must prioritize the deployment of low-latency, automated defense layers that reside as close to the source of the traffic as possible. Furthermore, internal resilience strategies should involve stress-testing network equipment against high-intensity, short-duration bursts to identify potential bottlenecks in the hardware itself. Moving forward, the most effective defense will involve a holistic combination of cloud-native scrubbing and hardened on-premise infrastructure, ensuring that connectivity remains stable despite the inevitable and increasingly frequent surges of malicious activity that characterize the modern digital era.