Kwame Zaire is a seasoned authority in industrial manufacturing, specializing in the intersection of high-performance electronics and production safety. With a career focused on the evolution of predictive maintenance and quality control, he has become a leading voice on how digital infrastructure transforms the factory floor. Today, he joins us to discuss the strategic integration of private 5G and AI-driven security, exploring how manufacturers can safeguard their data sovereignty and maintain seamless operations under the weight of modern regulatory demands and evolving cyber threats.
Generic IT security tools often create performance bottlenecks in industrial settings. How does the integration of AI-optimized firewalls with private 5G infrastructure maintain real-time performance, and what specific verification steps ensure that high throughput is not sacrificed for network resilience?
In the industrial world, every millisecond counts, and traditional security layers often introduce a lag that production managers simply cannot afford. By integrating AI-optimized next-generation firewalls directly into the private 5G infrastructure, we move security closer to the edge where the data is actually generated. We have performed extensive testing across multiple deployment scenarios to verify that high availability and network resilience are baked into the system from the start. This rigorous verification process ensures that the firewall can handle the massive data volumes of modern production without causing the performance degradation typically seen in standard IT solutions. It’s about creating a specialized environment where high throughput and low latency are protected, not hindered, by the security architecture.
Regulations like NIS2 and IEC 62443 demand robust defense-in-depth strategies for manufacturing. How does on-premises connectivity support data sovereignty, and what roles do deterministic wireless signals play in protecting worker safety while preventing costly production downtimes during a cyberattack?
Modern regulations are no longer just suggestions; they are strict mandates that require a defense-in-depth approach to protect critical infrastructure. On-premises connectivity is the cornerstone of this strategy because it ensures data sovereignty, keeping sensitive operational information entirely within the factory walls and independent of external mobile operators. By using deterministic wireless signals, we provide a stable and predictable communication path for mobile assets, which is vital for preventing the erratic behavior that leads to worker injuries or equipment damage. If an attack occurs, this localized control allows the system to maintain its integrity, preventing the cascading failures that result in millions of dollars in downtime. The goal is to build a fortress that remains operational even when the external digital landscape is under siege.
Continuous monitoring is vital for identifying unauthorized devices without interrupting live production. In what ways does passive, non-intrusive software detect communication anomalies, and how does this approach differ from active scanning methods that might impact sensitive real-time control applications?
Active scanning can be a nightmare for industrial control systems because the mere act of “pinging” a sensitive device can cause it to crash or misfire, halting the entire line. Instead, we utilize passive, non-intrusive software that essentially “listens” to the network traffic without ever interfering with the signals themselves. This software continuously monitors the environment for unauthorized devices or strange communication patterns that don’t belong in a steady-state production cycle. Because it is non-intrusive, we can identify threats in real-time while the machinery keeps humming along at full capacity. This difference is fundamental; it allows us to maintain a constant state of vigilance without the risk of accidentally triggering a production stoppage ourselves.
Industrial environments rely on specific OT protocols that standard security tools often fail to analyze. How does Layer 7 security facilitate deep packet inspection for these protocols, and what measures are taken to prevent malware or data exfiltration without causing the performance degradation typical of off-the-shelf tools?
Standard security tools often treat industrial traffic like a black box, but our approach uses Layer 7 security to perform deep packet inspection specifically for OT protocols. This means the firewall understands the “language” of the factory floor, allowing it to look inside the data packets to ensure they are legitimate commands rather than masked malware or attempts at data exfiltration. Because this technology is specifically optimized for industrial environments, it handles these complex inspections at the speed of the network. We’ve moved away from the “one size fits all” IT approach to a system that recognizes the specific signatures of industrial threats. This ensures that even as we stop intrusion attempts, the real-time control applications continue to receive their instructions without a heartbeat of delay.
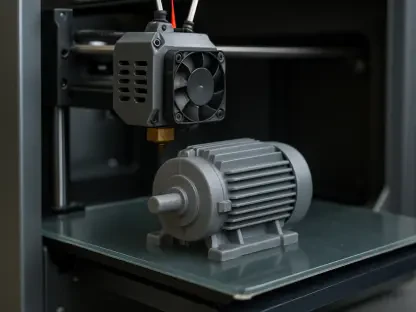
Data-driven production systems require wireless connectivity for a massive number of sensors and mobile assets. How should manufacturers prioritize the deployment of private 5G to manage these assets, and what steps are necessary to ensure the core network remains independent of external mobile operators?
The first step for any manufacturer is to identify the critical mobile and moving assets that require the highest level of reliability, such as autonomous robots or high-density sensor arrays. Private 5G provides the essential infrastructure for these assets because it offers a dedicated slice of spectrum that isn’t shared with the public. To ensure true independence, the core network infrastructure must be deployed on-site, allowing the manufacturer to manage their own security keys and traffic routing. By integrating built-in security features within this private core, we eliminate the reliance on external providers who might not prioritize industrial-grade uptime. This transition turns the network into a controlled utility, much like electricity or compressed air, that the factory owns and secures entirely on its own terms.
What is your forecast for the evolution of AI-driven cybersecurity in industrial 5G networks?
I believe we are moving toward a future where the network is essentially “self-healing,” where AI doesn’t just detect threats but anticipates them based on microscopic changes in signal behavior. As we connect a countless number of sensors, the volume of data will become too large for human teams to monitor, making AI-driven deep packet inspection the only viable way to maintain safety. We will see security becoming more deeply embedded into the hardware itself, where the 5G radio and the firewall operate as a single, intelligent organism. This evolution will allow factories to become even more autonomous, as the underlying infrastructure will have the “reflexes” to block malware and optimize performance in real-time without any human intervention. Industrial security will no longer be an add-on; it will be the very foundation upon which the next generation of global manufacturing is built.