Welcome to an eye-opening conversation on the evolving world of hacktivism and its impact on critical infrastructure. Today, we’re speaking with Kwame Zaire, a renowned expert in manufacturing with a deep focus on electronics, equipment, and production management. Kwame is also a thought leader in predictive maintenance, quality, and safety, bringing a unique perspective to the intersection of industrial systems and cybersecurity. In this interview, we’ll explore how hacktivists have shifted from simple digital disruptions to sophisticated attacks on vital systems, the reasons behind targeting industrial control systems (ICS), and the broader implications for public safety and national security. Join us as we unpack these pressing issues with Kwame’s expert insights.
How would you describe hacktivism, and in what ways have you seen its focus and tactics transform over the past few years?
Hacktivism, at its core, is a form of cyber activism where individuals or groups use hacking techniques to promote a social or political cause. A few years back, it was mostly about making loud, visible statements—think website defacements or Distributed Denial of Service (DDoS) attacks that would knock a site offline temporarily. These were more about embarrassment or disruption than deep damage. But recently, there’s been a clear shift. Hacktivists are now aiming for critical infrastructure, like energy grids or manufacturing systems, with much more advanced methods. Data breaches and access-based intrusions are on the rise, showing they’re after sensitive information or long-term control rather than just a quick headline. From an industrial perspective, this evolution is alarming because it targets the backbone of our daily operations—systems that, if compromised, could halt production or worse.
What do you believe is driving hacktivists to increasingly target critical infrastructure like energy or transportation systems?
Critical infrastructure is the lifeblood of any society—energy, transportation, water systems, and manufacturing keep everything running. That’s exactly why hacktivists are drawn to them. Disrupting these systems doesn’t just create a nuisance; it can cause widespread chaos, economic loss, and even threaten public safety. For instance, shutting down a power grid in winter could leave thousands without heat. From my experience in manufacturing, I’ve seen how interconnected these systems are, especially with the rise of IoT and integrated IT-OT environments. That connectivity, while efficient, creates vulnerabilities that hacktivists exploit to maximize impact and push their agendas, often tied to geopolitical tensions.
How does this move from simpler attacks like DDoS to more complex intrusions affect national security and public safety, especially in industrial sectors?
The shift to complex intrusions is a game-changer. A DDoS attack might slow down a website for a few hours, but gaining access to industrial control systems or breaching data in a manufacturing plant can have cascading effects. Imagine a hacker manipulating equipment settings in a factory—say, altering temperature controls in a chemical process. That could lead to explosions or toxic leaks, endangering workers and communities. On a national level, these attacks can erode trust in essential services and destabilize economies. For national security, it’s a direct threat because critical infrastructure is often tied to defense capabilities. We’re no longer just dealing with digital graffiti; these are attacks with real-world, physical consequences.
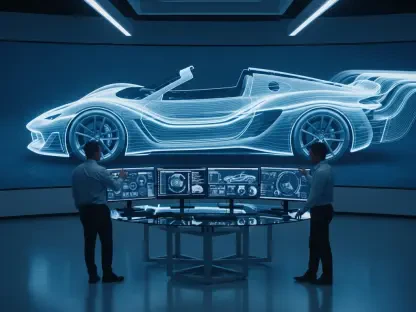
With Russia-linked groups reportedly leading the charge in targeting industrial control systems, what can you tell us about their strategies and why they might be so effective?
These groups have shown a highly structured approach, focusing on sustained campaigns rather than one-off hits. They often target energy infrastructure across multiple regions, which suggests they’re not just testing the waters but aiming to create systemic disruption. Their effectiveness comes from a mix of technical skill and psychological warfare. For example, posting screen recordings of them tampering with ICS controls isn’t just proof of access—it’s a deliberate tactic to instill fear and uncertainty in both the public and the targeted organizations. From a manufacturing standpoint, I can tell you that seeing someone manipulate your equipment remotely shakes confidence in system integrity, which can be as damaging as the attack itself.
Why do you think traditional tactics like DDoS attacks and website defacements remain so prevalent among hacktivists, even as newer methods emerge?
Traditional tactics like DDoS and defacements are still popular because they’re relatively easy to execute and don’t require the same level of technical expertise as, say, breaching an ICS. They’re the digital equivalent of a protest sign or graffiti—quick, visible, and effective for making a statement. In manufacturing, we often see smaller-scale disruptions used as a distraction while more sophisticated attacks are underway. These older methods still disrupt operations, especially for businesses reliant on online presence, and they can overload IT teams, creating openings for deeper intrusions. They’re not as devastating as data breaches or ICS attacks, but they remain a low-effort, high-visibility tool in the hacktivist toolkit.
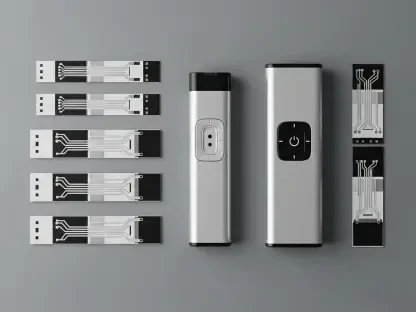
The trend toward access-based intrusions and data breaches seems significant. What does this tell us about the changing goals of hacktivists, especially in relation to industrial environments?
This trend points to a shift from disruption for the sake of attention to disruption for control and leverage. Gaining unauthorized access to networks or breaching data isn’t just about stealing information; it’s about holding power over a system. In industrial environments, this could mean accessing proprietary designs, production schedules, or even safety protocols. Hacktivists might use this to blackmail organizations, expose vulnerabilities publicly, or sabotage operations from the inside. It reflects a more strategic intent—less about making noise and more about inflicting lasting damage or gaining influence. From my perspective in production management, this is terrifying because it targets the very data and systems we rely on for safety and efficiency.
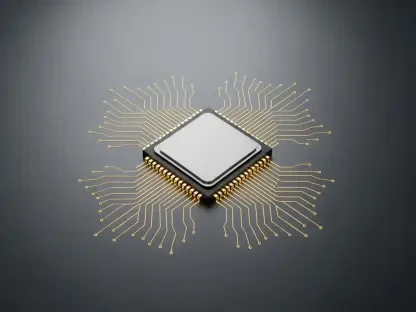
What is your forecast for the future of hacktivist threats against critical infrastructure, and how should industries like manufacturing prepare for what’s coming?
I foresee hacktivist threats becoming even more sophisticated and targeted as they continue to blur the lines between activism, cybercrime, and state-sponsored agendas. We’ll likely see more attacks on operational technology, especially as IT and OT systems become further integrated in industries like manufacturing. The psychological component will also grow—hacktivists will keep leveraging fear through publicizing their access. To prepare, industries need to prioritize robust cybersecurity, focusing on securing identities and access points with principles like least privilege and just-in-time access. Microsegmentation of systems can limit damage if a breach occurs, and regular vulnerability assessments are critical. Collaboration between IT and OT teams is non-negotiable—our safety and stability depend on it.