The modern workforce operates across a fragmented landscape where invisible devices and overlooked permissions create a playground for sophisticated digital adversaries. As organizations grapple with the reality that over half of their endpoints might be invisible to standard security protocols, the need for a unified, agentic defense has never been more pressing. Huntress has addressed this gap by expanding its platform to include Managed Endpoint Security Posture Management (ESPM) and Managed Identity Security Posture Management (ISPM).
These tools represent a departure from traditional, reactive monitoring by focusing on the underlying configurations that attackers exploit. By integrating expert-led oversight with automated remediation, businesses can now close the loop between detecting a threat and hardening the environment against its return. This evolution ensures that security is not just a series of alerts but a continuous state of resilience.
The Strategic Necessity of Automated Posture Management
Adopting modernized security posture management is no longer optional for organizations facing a sophisticated threat landscape. Relying on manual oversight in an era of rapid-fire exploits leads to inevitable gaps, as human teams cannot possibly track every minor configuration drift across thousands of identities and devices. Automated systems provide the necessary speed to counter these risks.
By shifting toward automation, companies achieve a significantly higher baseline of protection while optimizing their most valuable resource: time. Instead of chasing routine configuration fixes, internal IT teams can focus on high-level strategy. This proactive approach significantly reduces the likelihood of a breach, saving organizations from the astronomical recovery costs and reputational damage associated with ransomware.
Implementing Actionable Best Practices for Endpoint and Identity Hardening
Effective security requires a fundamental shift from reactive monitoring to proactive hardening. It is no longer enough to wait for an alert to trigger; instead, the digital environment must be made inherently hostile to attackers. Utilizing the latest capabilities in managed security allows for a more robust defense against common exploit vectors like unauthorized access and rogue software.
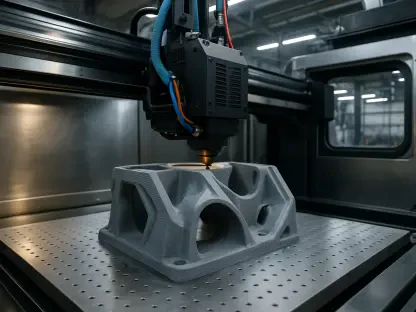
Reducing the Endpoint Attack Surface with Managed ESPM
Organizations should implement Managed ESPM to gain total control over software environments and system configurations. This practice involves utilizing real-time threat intelligence to block unauthorized applications before they can establish a foothold. By ensuring that core security settings are consistently applied across all devices, even those previously hidden from view, the overall risk profile of the company drops significantly.
Consider the common challenge of a mid-sized firm facing a surge in unauthorized remote monitoring tools. By deploying Managed ESPM, the organization automatically identifies and blocks these rogue RMM tools. This integration with Microsoft Defender allows for the remediation of vulnerabilities in real-time. Consequently, what once took days of compliance reporting is reduced to a few minutes of automated verification.
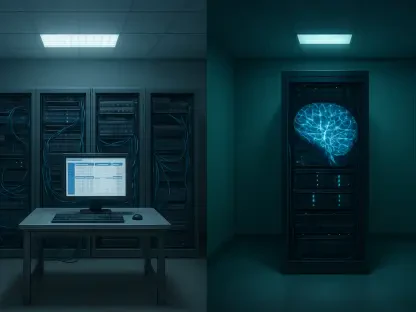
Securing Digital Identities within Cloud Ecosystems
Managed ISPM should be used to harden Microsoft 365 environments by enforcing strict identity policies. This practice focuses on eliminating excessive permissions and protecting against identity-based attacks like OAuth abuse. By ensuring that Entra ID and Conditional Access settings remain in a known-good state, the platform prevents attackers from leveraging stolen credentials to move laterally through the network.
When an unauthorized attempt to modify Conditional Access policies occurs, speed is the only effective defense. With Managed ISPM, the platform detects any deviation from the established security baseline and automatically rolls back the changes. This maintaining of a hardened posture occurs without requiring manual intervention from a security analyst, ensuring that the perimeter remains intact even during an active compromise attempt.
Final Evaluation: Who Benefits Most from Huntress’s New Capabilities?
The addition of Managed ESPM and ISPM represented a major leap forward for small to mid-sized organizations that lacked the resources for a massive, in-house Security Operations Center. By synthesizing complex data into automated, actionable protection, Huntress bridged the gap between enterprise-grade security and mid-market accessibility. Organizations heavily reliant on Microsoft 365 found these tools particularly transformative for managing shadow endpoints.
Moving forward, stakeholders should evaluate their current integration levels with Microsoft Defender and Entra ID to ensure they can fully capitalize on these automated features. Future security strategies will likely move toward even deeper agentic autonomy, where the system not only repairs known issues but anticipates configuration needs based on emerging global threat patterns. Adopting these tools today positioned businesses to handle the increasingly complex identity and endpoint challenges of tomorrow.