The rapid convergence of industrial automation and digital connectivity has left many critical infrastructure sites vulnerable to sophisticated cyber attacks that bypass traditional perimeter defenses. As the demand for remote maintenance grows, the Privileged Remote Operations (PRO) framework emerges as a vital evolution in how organizations manage sensitive access. This system moves beyond simple encrypted tunnels by placing identity and context at the center of every connection. It addresses the fundamental friction between the need for high-speed operational efficiency and the stringent security requirements of the modern industrial landscape.
Understanding Privileged Remote Operations and the Cyolo PRO Framework
Traditional access methods often fail in Operational Technology (OT) because they rely on broad network visibility that permits lateral movement. The PRO framework shifts this paradigm by implementing Zero Trust principles directly at the application layer. This means no user is trusted by default, regardless of their location on the network. By enforcing secure identity verification, the system ensures that only authenticated personnel can interact with specific industrial controllers, effectively shrinking the attack surface to the smallest possible point.
Maintaining critical infrastructure now requires a delicate balance of providing vendor access while protecting physical assets. The relevance of this technology lies in its ability to offer granular control over these remote sessions. Instead of granting a maintenance contractor full network access, the PRO framework creates a secure, isolated path to a single piece of equipment. This approach is essential for preventing the kind of wide-scale disruptions that have recently plagued energy and water sectors globally.
Core Pillars of Modern Remote Security
AI-Powered Session Intelligence
One of the most transformative elements of this review is the integration of artificial intelligence to modernize the auditing process. Historically, security teams had to spend hours watching video recordings of remote sessions to identify potential errors or malicious acts. The AI-powered engine replaces this manual labor by generating searchable transcripts and categorizing user behavior in real-time. It detects anomalies—such as an unauthorized command or an unusual configuration change—allowing for immediate intervention rather than a post-incident autopsy.
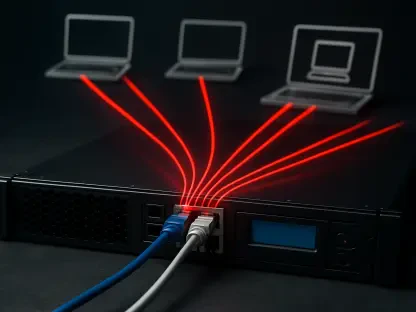
Passive OT Asset and Traffic Discovery
The Fabric Controller represents a significant technical leap by offering deep visibility without the risks associated with intrusive software agents. By collecting telemetry data directly from existing network switches, the system maps communication paths as they occur. This passive approach is crucial for OT environments where even a minor software conflict could cause a physical equipment failure. It effectively illuminates “shadow access,” revealing hidden connections that administrators might have otherwise overlooked, ensuring the security map matches the physical reality.
Centralized Management and Unified Dashboards
Complexity is often the enemy of security, which is why the unified dashboard is such a critical component. It synthesizes vast amounts of data—ranging from active identity sources to ongoing approval workflows—into a clear, actionable interface. This centralization allows administrators to see the entire operational landscape at a glance. By streamlining these complex data streams, the platform reduces the likelihood of human error, ensuring that security policies are applied consistently across all global sites.
Emerging Trends in Secure Industrial Connectivity
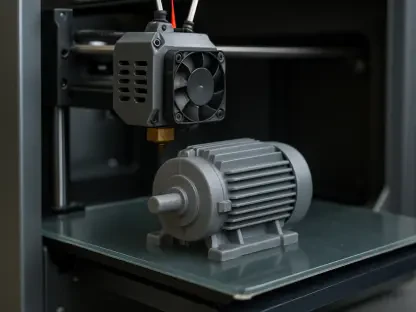
The industry is currently witnessing a definitive move toward agentless architectures that prioritize non-disruptive deployment. Manufacturing and energy sectors are increasingly rejecting tools that require modifications to sensitive legacy hardware. This trend reflects a broader desire for “invisible” security that protects the environment without slowing down production cycles. Furthermore, the once-distinct worlds of IT and OT security protocols are converging into a singular defense perimeter, allowing for a more cohesive organizational strategy.
Real-World Applications in Critical Infrastructure
In practical terms, this technology is already proving its worth in sectors like water treatment and energy distribution. For example, a technician located across the globe can now troubleshoot a malfunctioning pump without ever gaining access to the wider corporate network. These use cases demonstrate how AI-driven oversight helps companies meet rigid regulatory standards. By providing forensic-grade logging and automated auditing, organizations can prove compliance with international safety standards while maintaining their operational pace.
Navigating Implementation Challenges and Limitations
Despite its advancements, the technology faces hurdles when integrating with ancient, proprietary protocols found in decades-old industrial equipment. Some legacy systems lack the basic communication standards required for modern telemetry, forcing organizations to invest in hardware bridges. Additionally, the initial cost of a comprehensive security upgrade can be a barrier for smaller utilities. Ongoing development is focusing on expanding the compatibility of passive discovery tools to ensure even the oldest machinery can be brought under a secure umbrella.
The Future of Remote Operational Integrity
Looking ahead, the focus is shifting toward predictive security measures that utilize machine learning to anticipate breaches before they manifest. As the Industrial Internet of Things (IIoT) expands, the sheer number of connected devices will require even more automated oversight to prevent massive supply chain disruptions. The long-term impact of this technology will likely be a self-healing security environment where the system automatically revokes access at the first sign of a compromised credential or an abnormal traffic pattern.
Summary of the Privileged Remote Operations Review
The transition of remote access from a simple connectivity utility to a strategic asset for operational integrity was the defining theme of this analysis. The framework successfully demonstrated that security does not have to come at the expense of productivity, provided that the tools are built specifically for the unique constraints of OT. Organizations that adopted these measures found themselves better equipped to handle the complexities of a hyper-connected industrial world. Future advancements should focus on lowering the barrier to entry for smaller enterprises to ensure global infrastructure remains resilient.