In an era where the boundary between the physical and digital worlds has all but vanished, Kwame Zaire stands as a leading voice in securing the complex machinery that powers modern industry. With a background rooted in manufacturing and electronic equipment, he brings a pragmatic, hands-on perspective to the escalating threats facing our connected infrastructure. Today, we explore how the rapid evolution of specialized devices—from medical imaging tools to industrial converters—has fundamentally altered the attack surface, creating a landscape where traditional perimeter defenses are no longer enough to keep an organization safe.
Throughout our conversation, we delve into the shifting nature of high-risk hardware, the alarming density of vulnerabilities found in core network components like routers, and the resurgence of outdated protocols that leave doors wide open for intruders. We also examine the critical need for “containment as control” to prevent malware from jumping between IT and operational environments.
With nearly 75% of the highest-risk devices changing in just two years, what operational challenges do new entries like serial-to-IP converters or RFID readers present? How do these “softer” entry points allow attackers to bypass perimeter security and move laterally across a corporate network?
The sheer velocity of this shift is staggering; when 75% of the threat landscape changes in just 24 months, most security teams struggle just to maintain an accurate inventory. These devices, such as serial-to-IP converters and RFID readers, are often “unmanaged and unagented,” meaning they don’t run traditional security software that would alert a technician to a breach. Because they frequently utilize embedded management interfaces that are rarely monitored, they become invisible stepping stones for an intruder. Once an attacker gains a foothold on one of these softer points, they can exploit “east-west” traffic, moving sideways through the network while completely bypassing the heavy guards we’ve placed at the front door. It’s a sensory nightmare for a facility manager because these devices are essential for production but were never built with modern hardening or consistent patching in mind.
Network infrastructure like routers and switches now average 32 vulnerabilities per device, often surpassing traditional computers in risk. Why are these core components becoming primary targets for critical vulnerabilities, and what specific steps should teams take to prioritize patching these over traditional endpoints?
Routers have officially surpassed computers in terms of risk, now accounting for a full one-third of the most critical vulnerabilities found in organizational networks. This happens because these devices are the literal backbone of the environment, yet they are often overlooked in standard patch cycles compared to a high-profile laptop or server. When a single router averages 32 vulnerabilities, it becomes a goldmine for an attacker looking for a persistent, high-privileged position. Teams must pivot their strategy to prioritize network infrastructure by identifying these core assets and treating them with the same urgency as a primary database. We have to move away from the “set it and forget it” mentality for switches and routers, ensuring they are integrated into automated patch management programs immediately.
Specialized hardware like medication dispensing systems and BACnet routers often lack consistent hardening or monitoring. How does the presence of default credentials and embedded interfaces in these devices complicate inventory management, and what protocols should be implemented to ensure these isolated systems don’t become gateways for ransomware?
The presence of default credentials on a medication dispensing system or a BACnet router is like leaving the keys in the ignition of an armored truck. These devices are highly specialized, often running niche operating systems that don’t play well with standard IT discovery tools, which makes even knowing they exist a monumental challenge. Because they rely on embedded interfaces that are rarely updated, they offer a wide-open path for ransomware to migrate from a simple office network into life-critical medical systems or building automation. To counter this, organizations must implement strict network segmentation and zero-trust protocols specifically for IoMT and OT devices. We need to move toward a model where every device is authenticated and monitored for anomalous behavior, regardless of its specialized function.
The end of support for legacy operating systems is coinciding with a surprising rise in unencrypted Telnet usage across many sectors. How does this combination of outdated firmware and insecure protocols create a “perfect storm” for attackers, and what is the most effective way to transition away from these vulnerabilities?
We are currently facing a “perfect storm” where the end of Windows 10 support is pushing more systems into the legacy category just as we see a spike in unencrypted Telnet usage. It is deeply concerning to see Telnet rising across multiple sectors, as it transmits data in plain text, allowing any attacker on the network to sniff out passwords and sensitive commands. When you pair this with printers, switches, and IP phones that are already running outdated or unsupported firmware, you create an environment that is trivial to exploit. The most effective transition involves a dual-track approach: aggressively replacing the oldest hardware while simultaneously enforcing the use of encrypted protocols like SSH, which is fortunately becoming the second most common protocol observed. We have to stop viewing firmware updates as “optional maintenance” and start seeing them as a fundamental requirement for staying online.
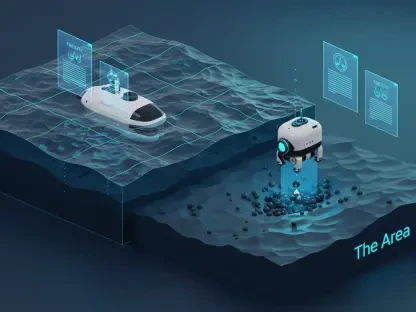
As attackers increasingly pivot from IT networks into OT workstations or medical printers, the focus is shifting toward “containment as control.” How can organizations automatically limit the blast radius once a device is compromised, and what metrics should security leaders use to measure the effectiveness of their lateral movement defenses?
In today’s volatile threat landscape, we have to assume that a device will eventually be compromised; therefore, containment is the new control. Organizations can limit the blast radius by using automated security platforms that can instantly isolate a device the moment it displays suspicious “east-west” movement, such as a printer suddenly trying to access an industrial workstation. Security leaders should measure their effectiveness by tracking the “dwell time” of an intruder and the number of hops an attacker is able to take before being blocked. If a malware strain jumps from an IT network into a medical image printer, the metric for success is how quickly that printer was siloed from the rest of the clinical environment. We need to shift our focus from just building higher walls to creating internal “firebreaks” that prevent a single breach from becoming a total catastrophe.
What is your forecast for connected device security?
I foresee a future where the distinction between “IT security” and “device security” disappears entirely, replaced by a unified, automated risk management framework. As we see more of these 11 new high-risk device types—like DICOM gateways and power distribution units—enter the fold, the manual way of managing security will simply collapse under the weight of complexity. We will see a massive push toward “self-healing” networks where AI-driven controls identify, prioritize, and remediate vulnerabilities in real-time across all domains. Organizations that fail to adopt these automated, adaptive strategies will find themselves constantly one step behind attackers who are already leveraging routers and IP cameras as primary weapons. Ultimately, the winners will be those who can maintain total visibility and stop lateral movement before it reaches the heart of their operations.