The global industrial sector has officially surpassed all other commercial categories to become the primary focus of sophisticated digital extortion and state-sponsored sabotage. For the fifth consecutive year, the manufacturing industry has claimed the top spot as the most targeted sector for cyber threats, according to data available in 2026. Recent market analysis confirms that nearly 28 percent of all documented attacks now focus on industrial production and global supply chains. This trend is not a mere coincidence; it is the result of a “perfect storm” where aging infrastructure meets rapid, sometimes reckless, digitization. As manufacturing plants transition from isolated hubs into hyper-connected environments, they offer a lucrative and high-stakes playground for cybercriminals. This analysis explores the architectural vulnerabilities, economic motivations, and technological shifts that have placed global production lines in the crosshairs of sophisticated adversaries.
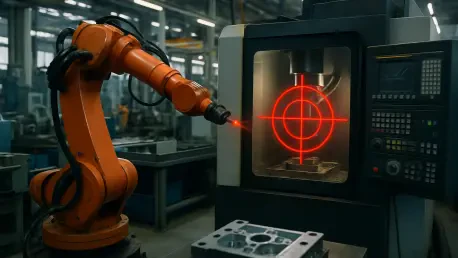
The Growing Bullseye on the Factory Floor
The intensification of threats against the manufacturing sector reflects a fundamental shift in the risk appetite of global threat actors. Unlike the financial sector, which has spent decades hardening its digital perimeters, the industrial world has historically prioritized physical safety and continuous uptime over cybersecurity. This cultural focus created a massive gap in defense maturity that attackers are now exploiting with alarming regularity. The sheer scale of the target is massive, encompassing everything from automotive assembly lines and pharmaceutical labs to food processing plants and heavy machinery manufacturing.
The vulnerability is further compounded by the high cost of downtime. In the manufacturing world, every minute of a stalled assembly line translates into thousands of dollars in lost revenue and potential contractual penalties. Cybercriminals have recognized that this “operational urgency” makes manufacturers far more likely to pay high ransoms quickly to restore operations. Consequently, the industry has become a primary laboratory for testing new extortion techniques, including multi-tier pressure tactics where attackers simultaneously encrypt data, threaten to leak intellectual property, and target a company’s downstream customers.
From Isolation to Integration: The Evolution of Industrial Risk
Historically, manufacturing facilities operated under a principle known as “air-gapping,” where machines were physically disconnected from the internet. Industrial protocols were proprietary and obscure, requiring specialized knowledge to manipulate. This isolation provided a natural layer of security; to sabotage a machine, an attacker usually needed physical access to the premises. However, the relentless drive for efficiency has dismantled these physical barriers. The pursuit of real-time data analytics, predictive maintenance, and seamless supply chain integration required connecting the factory floor, often referred to as Operational Technology (OT), directly to the corporate network and the cloud.
While this integration has unlocked unprecedented productivity, it has also exposed legacy systems designed decades ago to modern, internet-scale threats. Many of the controllers and sensors currently in use were never built with security as a primary consideration because they were never meant to be reachable from the outside world. Today, a vulnerability in a remote-access portal or an office workstation can serve as a bridge into the most sensitive areas of a production facility. This erosion of the digital perimeter means that a cyberattack is no longer just a threat to data; it is a threat to the physical integrity of the manufacturing process itself.
The Convergence of Legacy Software and Modern Exploitation
The Fatal Flaws of Memory-Unsafe Code
At the heart of many industrial vulnerabilities lies a technical debt dating back to the inception of modern automation. Most industrial controllers, sensors, and edge devices rely on code written in C or C++. While these languages are highly efficient for hardware control and real-time processing, they are categorized as “memory unsafe.” This technical designation means the languages are prone to flaws like buffer overflows, which allow attackers to inject malicious code directly into a system’s memory. In the modern context, these vulnerabilities account for up to 70 percent of all exploitable flaws in embedded systems. Because these machines have lifecycles spanning 20 to 30 years, manufacturers are often stuck with “soft underbellies” that are nearly impossible to patch without replacing the hardware itself, leading to a persistent and widespread risk profile.
The Rise of AI-Driven Reconnaissance
The economics of cyberattacks have shifted dramatically with the widespread adoption of Artificial Intelligence. In the past, identifying a specific vulnerability in a complex, multi-site manufacturing plant required a human attacker to perform weeks of manual reconnaissance and testing. Today, AI-powered tools can scan global manufacturing estates in a matter of hours, identifying unpatched public-facing applications and outdated software with surgical precision. This automation has effectively closed the “patching window” for defenders. While plant managers struggle to find maintenance downtime to update systems without halting production, AI-driven bots are already knocking on the digital door, looking for the single weakest link in the perimeter.
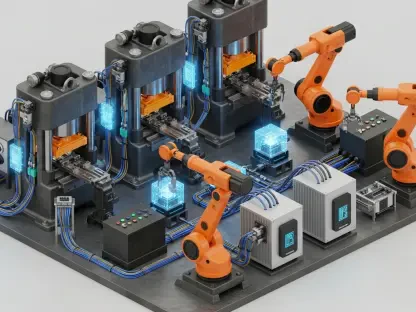
The Fragility of the Global Software Supply Chain
Modern manufacturing equipment is rarely the product of a single company; it is a collage of third-party software, open-source libraries, and specialized firmware. This interconnectedness has birthed a massive blind spot: the software supply chain. Attackers have realized that instead of breaching a thousand individual factories, they only need to compromise one software vendor that provides code to those thousand factories. These “downstream” attacks have increased fourfold in recent years, turning trusted software updates into Trojan horses. Many manufacturers currently lack a comprehensive Software Bill of Materials (SBOM), meaning they often do not even know which third-party components are running inside their most critical assembly line robots, making it impossible to defend against hidden risks proactively.
Emerging Threats and the Future of Industrial Sabotage
As the threat landscape matures, the nature of these attacks is moving from simple data theft toward “kinetic impact”—attacks that cause physical damage or environmental disasters. There is a documented rise in “pre-positioning,” where nation-state actors infiltrate networks not to steal information, but to remain dormant until a geopolitical conflict provides a reason to sabotage power grids or production lines. This shift from financial crime to potential warfare highlights the strategic importance of manufacturing. Furthermore, the convergence of ransomware and sabotage is creating new categories of risk where the goal is not just money, but the total disruption of a competitor’s market share or a nation’s economic stability.
Strategies for a Resilient Manufacturing Ecosystem
To combat these evolving threats, the industry must move beyond the “patch-and-pray” model. A multi-layered defense strategy is essential for survival in this environment. First, manufacturers must implement “security by design,” ensuring that new equipment is either built with modern, memory-safe languages or protected by runtime security layers that block exploits without requiring a system reboot. Second, visibility must become a top priority; adopting SBOMs allows companies to map their software dependencies and react instantly when a vulnerability is announced. Finally, the cultural gap between IT and OT must be closed once and for all. Cybersecurity can no longer be viewed as an office-based IT task; it must be treated as a core safety requirement on the factory floor, as vital as hard hats and safety goggles.
Securing the Heartbeat of Global Production
The investigation into the surge of cyberattacks against the manufacturing sector revealed that the division between digital code and physical machinery had effectively vanished. Stakeholders recognized that adversaries were no longer satisfied with stealing credentials; they focused their efforts on the physical engines of the global economy. The transition toward integrated security protocols became a mandatory evolution for those who intended to survive the digital shift. Industry leaders identified that the adoption of memory-safe technologies and the implementation of transparent supply chain practices were the only viable paths forward. By treating digital integrity as a core operational safety standard, the manufacturing world began to reclaim its resilience. This proactive stance ensured that the physical engines of global commerce remained operational, even as the digital world became increasingly volatile. Significant investments in automated monitoring and the widespread use of software transparency tools finally provided the visibility necessary to defend complex industrial estates. The sector learned that in a connected world, the safety of the production line was inseparable from the security of the code that governed it.