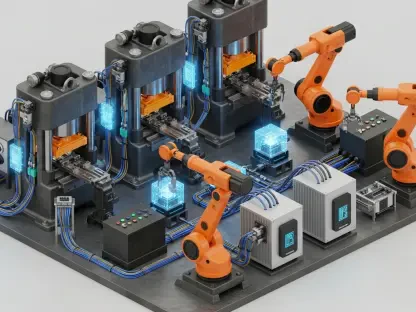
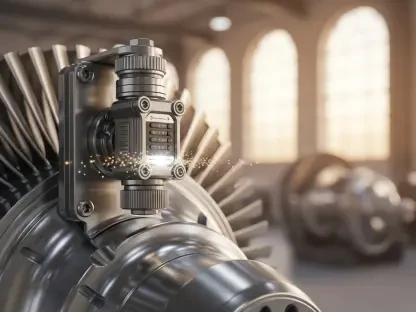
Industrial systems across the globe are facing an unprecedented level of sophisticated cyber threats as the historical boundaries between information technology and operational technology continue to dissolve rapidly. While the integration of these environments offers significant efficiency gains, it also exposes industrial control systems and manufacturing floors to risks that were previously mitigated by physical isolation or simple air-gapping. AppGate has recently introduced a specialized Zero Trust Network Access solution designed specifically for these high-stakes industrial environments to replace aging virtual private network technologies. By transitioning from a traditional perimeter-based defense to an identity-centric model, this new offering aims to provide granular control over who can access specific industrial assets. Unlike legacy systems that often grant broad network visibility once a user is authenticated, this approach ensures that every connection is verified and authorized on a per-session basis, effectively hiding sensitive equipment from potential lateral movement.
The Shift Toward Identity-Centric Industrial Security
The reliance on traditional Virtual Private Networks in industrial settings has increasingly become a strategic liability for operators of energy facilities and manufacturing plants. These legacy tools were designed for a different era of connectivity where remote access was infrequent and the internal network was assumed to be safe. However, once a contractor or employee gains entry through a standard VPN, they typically receive far more visibility into the broader network than is necessary for their specific tasks. This over-privileged access creates a massive attack surface where a single compromised credential can lead to the disruption of entire production lines or critical utilities. AppGate’s solution addresses this fundamental flaw by enforcing strict policies before any network connection is even attempted. This shift ensures that the underlying infrastructure is never exposed to the public internet, reducing the likelihood of automated scanning and targeted exploitation that often precedes major industrial cyber incidents.
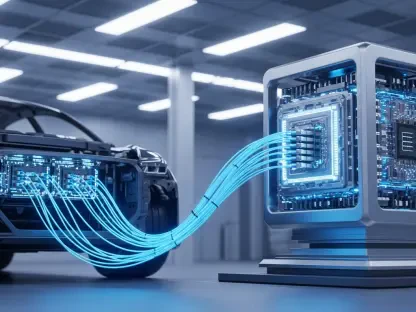
The deployment of this specialized Zero Trust architecture represented a definitive move toward more resilient and invisible industrial perimeters. Organizations that adopted these identity-centric strategies successfully minimized their exposure to the vulnerabilities inherent in legacy remote access tools. Moving forward, industrial operators should prioritize the integration of identity-based policies within their broader risk management frameworks to stay ahead of evolving threats. Technical leaders recognized that the key to long-term stability lay in decoupling access from the physical network location, ensuring that security protocols did not hinder operational efficiency. Future efforts must focus on automating the verification processes across diverse hardware ecosystems to further reduce manual intervention. By investing in direct-routed connectivity and granular access controls, companies established a foundation for secure digital transformation that protected both their digital assets and physical infrastructure to ensure long-term stability.