The modern digital perimeter has dissolved into a complex web where the majority of network traffic no longer originates from a human finger tapping a screen but from independent code executing complex logic. This fundamental shift marks the arrival of Autonomous AI Identity Management, a paradigm designed to govern the burgeoning population of AI agents currently saturating enterprise ecosystems. As these agents transition from simple scripts to sophisticated decision-makers, traditional security methods have become remarkably obsolete, necessitating a new architectural foundation that moves beyond static credentials toward dynamic systems verifying machine intent.
The Evolution of Identity and Access Management for AI
Autonomous AI Identity Management represents the necessary response to the explosive growth of machine-to-machine authentication. Historically, non-human identities were treated as secondary service accounts tucked away in application code. However, the emergence of autonomous agents that can manage code, conduct research, or execute financial transactions has forced a total reevaluation of the trust model.
As organizations shift from human-centric security to automated workload protection, the focus has landed squarely on granular identity verification. This transition is not merely a technical upgrade but a cultural shift in how permissions are granted. Security teams now recognize that an AI agent operating with human-level privileges without equivalent oversight is a recipe for failure, birthng a field where identity is a cryptographic certificate of an agent’s purpose.
Core Components of AI-Specific Identity Frameworks
Dedicated Workload Identities: A New Standard
Assigning unique identities to specific AI agents provides a level of granularity previously impossible with shared service accounts. When each agent possesses its own distinct cryptographic footprint, security teams can track performance and resource consumption with surgical precision. This isolation ensures that if one agent malfunctions or is compromised, the blast radius is contained within that specific workload.
Furthermore, dedicated identities facilitate better auditing by providing a clear trail of which specific process initiated a request. This replaces the old method where multiple applications might hide behind a single service account, making it impossible to diagnose issues. By decoupling agents from the systems they inhabit, organizations create a more resilient architecture that treats every autonomous action as a verifiable event.
Identity-Bound Access Control: Task-Specific Security
Technical binding involves anchoring permissions directly to the functional profile of the AI agent rather than a broad role. This means an agent designed for data analysis cannot pivot to network configuration because its identity is mathematically restricted to specific task boundaries. This constraint-based approach ensures behavior remains within authorized boundaries even during unexpected environmental variables.
Such frameworks prioritize the principle of least privilege by default, making security an inherent part of the agent’s lifecycle. By maintaining these strict boundaries, developers can deploy autonomous systems with the confidence that the code will not exceed its mandate. This prevents the common issue of privilege creep, where agents accumulate excessive access over time.
Real-Time Policy Enforcement: Dynamic Session Management
Moving beyond static credentials, modern autonomous systems employ active session management that responds to environmental cues in real time. Static tokens are insufficient because an agent’s risk profile can change within milliseconds of a new interaction. Dynamic enforcement allows the system to revoke or modify permissions instantly if behavior deviates from established patterns.
This shift represents a significant move toward automated governance where security policies are as agile as the agents they manage. By integrating real-time feedback loops, organizations maintain a high level of security without hindering operational speed. Such systems ensure that access is never a permanent state but a continuous negotiation between the agent and the security authority.
Current Trends in Autonomous Security and Industry Gaps
The industry is seeing a pivot toward “Identity-First” security, yet there remains a profound struggle to distinguish human activity from autonomous actions. This visibility gap creates a blind spot where a significant portion of organizational activity occurs in a “gray area” eluding traditional monitoring tools. Furthermore, decentralized ownership has led to internal friction between security and development departments over governance responsibilities.
Real-World Applications and Sector Deployment
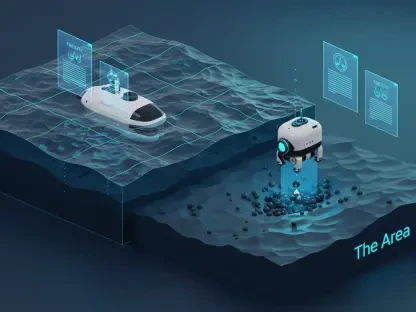
In software development, autonomous identity management supports modern DevOps pipelines where agents handle code reviews and deployment triggers. Beyond development, automated research and security monitoring see widespread deployment. Organizations use AI to scan for vulnerabilities, requiring agents to interact with external databases securely. The need for verified machine identity in these scenarios is paramount to prevent data leaks.
Technical Hurdles and Regulatory Obstacles
One pressing challenge is the prevalence of over-privileged access in legacy cloud environments not designed for granular machine identities. This leads to agents inheriting excessive power from the accounts they mirror. Regulatory obstacles also complicate the landscape, as unified IAM standards for autonomous agents are still in their infancy, forcing companies to build custom, often fragile, solutions to manage workloads.
Future Outlook and Technological Breakthroughs
The next wave of breakthroughs will transition from reactive measures like token revocation to proactive security orchestration. Future systems will utilize AI to secure AI, creating a self-healing identity mesh that mitigates risks before they can be exploited. Breakthroughs in automated audit trails will provide transparency into autonomous decision-making, leading to global cybersecurity resilience where machine identity is as unique as a fingerprint.
Final Assessment of Autonomous Identity Management
The investigation into the state of autonomous identity management revealed a significant disparity between the rapid adoption of AI agents and the maturity of governing frameworks. It was found that most organizations operated in a state of high risk, relying on outdated human-centric models to manage complex machine interactions. The data suggested that visibility gaps and fragmented ownership were the greatest inhibitors to secure scaling. Ultimately, the success of autonomous systems was determined by the willingness of enterprises to embrace dedicated machine identity controls over legacy practices. Future resilience depended on the implementation of real-time, identity-bound policies that could match the speed and autonomy of the agents they were designed to protect.