Kwame Zaire is a distinguished voice in the world of industrial electronics and production management, known for his deep focus on bridging the gap between operational technology and advanced networking. With years of experience navigating the complexities of predictive maintenance and equipment safety, Zaire has become a leading advocate for ruggedized, intelligent infrastructure in the manufacturing sector. In this conversation, we explore the evolution of industrial connectivity, focusing on the consolidation of hardware in extreme environments, the logistical transition toward private 5G networks, and the transformative impact of local edge computing. We also delve into the critical importance of supply chain security and how the integration of large language models is redefining the role of the modern network engineer.
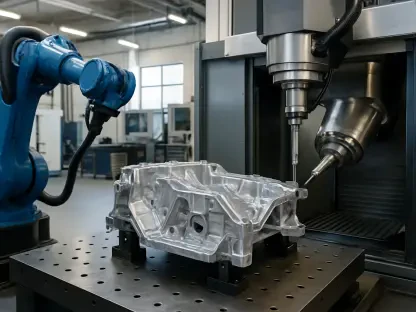
Field cabinets often lack space for multiple networking devices while facing extreme temperatures and hazardous conditions. How do you design hardware to consolidate switching and compute into one ruggedized platform, and what specific reliability benefits does this provide for teams managing critical infrastructure?
When you are working in the field, every square inch of a cabinet is precious real estate, and the environmental stakes are incredibly high. By integrating four Gigabit Ethernet ports directly into a single ruggedized platform, we effectively eliminate the need for standalone external switches, which are often the first things to fail in high-vibration or dusty environments. This design is built to endure the brutal swing from -40 °C winters to +75 °C summers, supported by rigorous certifications like ATEX, C1D2, and MIL-STD-810H. For the teams on the ground, this consolidation means fewer points of failure and a significantly simplified installation process. It transforms a cluttered, heat-trapping box of wires into a streamlined, reliable hub that can withstand the harshest industrial conditions without a second thought.
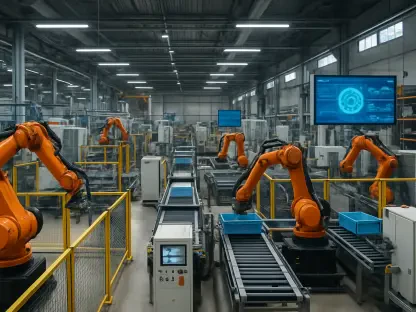
Critical infrastructure operators are increasingly moving toward private wireless networks like CBRS and Anterix. What logistical challenges do organizations face when transitioning from public carriers to private LTE, and how should they structure their hardware architecture to remain flexible as 5G RedCap and eMBB evolve?
The shift toward private spectrum is a game-changer for reliability, but the logistical hurdle usually lies in avoiding hardware obsolescence during the transition. Organizations need a unified hardware architecture that supports a variety of SKUs, allowing them to standardize on one platform while toggling between LTE, 5G RedCap, and 5G eMBB as their needs change. By having native support for Anterix, CBRS, and FirstNet, operators can finally step away from the unpredictability of public carrier congestion. This flexibility ensures that a utility company can deploy a secure, private network today and still have the headroom to scale up to high-bandwidth applications in five years. It is about building a long-term infrastructure commitment that matches the decades-long lifecycles common in the industrial world.
Modern SCADA integration and edge analytics require significant local processing power to reduce latency. How can teams effectively deploy Linux containers for platforms like AWS IoT Greengrass on a router, and what are the practical steps for reducing bandwidth costs by processing telemetry data locally?
To make edge computing actually work in a mission-critical setting, you need a powerful quad-core processor that can handle heavy lifting right at the source. By deploying Linux containers for platforms like AWS IoT Greengrass or Microsoft Azure IoT directly on the router, teams can move away from the “cloud-first” model that often leads to high latency and massive data bills. Instead of sending every single telemetry heartbeat to a remote server, the router processes that data locally and only transmits the critical anomalies or summarized reports. This localized intelligence means that if a sensor detects a dangerous pressure spike, the system can trigger a shutdown in milliseconds rather than waiting for a round-trip to a data center. It fundamentally changes the economics of the operation by slashing bandwidth consumption while simultaneously boosting the speed of decision-making.
Government agencies face strict procurement requirements and the logistical burden of physical SIM swaps in the field. How do TAA-compliant components and GSMA-compliant eSIM technology simplify zero-touch provisioning, and what security advantages do Western-made cellular modules provide to sensitive utility networks?
Security in critical infrastructure is only as strong as its weakest link, which is why we emphasize the use of Western-made cellular modules and TAA-compliant components for government-grade deployments. The logistical nightmare of sending a technician to a remote site for a physical SIM swap is now being replaced by GSMA SGP.32-compliant eSIM technology. This allows for a “live bootstrap” where a device can be pre-loaded and provisioned over the air without any human intervention on-site. This zero-touch approach doesn’t just save on truck rolls; it secures the supply chain by ensuring the hardware is configured in a controlled environment. For sensitive utility networks, this means a much smaller attack surface and the ability to switch carriers remotely if a network provider experiences an outage or a security breach.
Integrating large language models into device management allows for natural language troubleshooting and configuration insights. What does the workflow look like when using an AI assistant to query a massive device fleet, and how does this capability change the daily responsibilities of network engineers?
The introduction of an MCP server to bridge the gap between your device fleet and a large language model like Claude is a total paradigm shift. Instead of an engineer spending hours digging through logs and spreadsheets to find a misconfigured router, they can simply ask the AI, “Which devices in the eastern sector have experienced a drop in signal strength over the last 24 hours?” The AI queries the management platform, analyzes the telemetry, and provides a conversational summary with actionable configuration insights. This moves the engineer’s role from a reactive troubleshooter to a high-level strategist who manages by intent rather than manual CLI commands. It feels less like operating a machine and more like managing a digital workforce that can automate workflows and identify patterns that a human eye would likely miss.
What is your forecast for AI-driven operations in industrial networking?
I believe we are entering an era where the network will become entirely self-healing, moving from simple automation to true predictive autonomy. In the next few years, AI won’t just tell you that a device failed; it will have already rerouted traffic and adjusted power settings to prevent the failure before it even occurred. We will see natural language interfaces become the standard for all industrial deployments, making complex configurations accessible to field technicians who aren’t necessarily networking experts. This evolution will bridge the final gap between IT and OT, creating a seamless, intelligent fabric that treats the entire global fleet of devices as a single, responsive organism. The router will no longer be a passive tool, but a proactive partner in ensuring the uptime and safety of our most critical global systems.