The rapid digitization of global industrial networks has fundamentally altered the risk landscape for critical infrastructure providers by exposing once-isolated systems to a new generation of sophisticated, software-driven threats that bypass traditional perimeter defenses. In this landscape, the security of power grids, water utilities, and manufacturing plants is no longer a matter of simple physical locks or isolated local area networks. As these systems integrate with cloud environments and enterprise IT frameworks, the potential for catastrophic failure increases. NVIDIA is positioning its accelerated computing platform as the foundational pillar for a modern defense strategy that leverages artificial intelligence and specialized hardware. By embedding security directly into the underlying silicon of the infrastructure, the industry is moving toward a proactive model where threats are neutralized before they can impact physical operations. This transition is essential for maintaining the reliability of the services upon which modern society depends.
Architectural Evolution: Moving Beyond the Traditional Air Gap
The historical reliance on “air-gapping”—the practice of keeping industrial control systems entirely disconnected from the public internet—has become an obsolete strategy in a world that demands real-time data and remote operational oversight. Modern industrial facilities now require constant connectivity to optimize supply chains and monitor equipment health, but this connectivity creates a “security gap” where legacy hardware meets modern malware. Many of these physical systems were designed to operate for decades, often utilizing protocols that lack basic encryption or authentication mechanisms. Consequently, a breach in an enterprise network can now migrate laterally into the operational technology environment, potentially allowing unauthorized actors to manipulate physical processes. Addressing this vulnerability requires a departure from reactive software patches toward an architectural framework that treats security as an intrinsic part of the network’s data path, ensuring that connectivity does not come at the expense of safety.
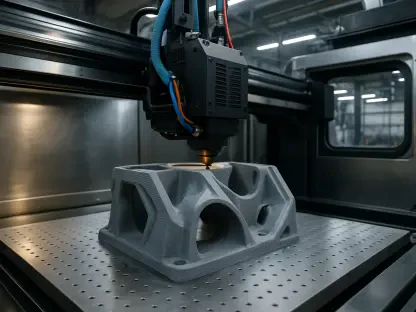
Central to this architectural shift is the implementation of the NVIDIA BlueField Data Processing Unit, which serves as a dedicated engine for offloading complex security tasks from the primary central processing unit. By isolating functions such as high-speed encryption, deep packet inspection, and stateful firewalling onto the DPU, organizations can protect their infrastructure without degrading the performance of time-sensitive industrial applications. This hardware-level isolation ensures that even if a host system is compromised, the security enforcement point remains independent and resilient. This approach allows for the deployment of a distributed defense-in-depth strategy where every network node acts as a micro-perimeter. By offloading these intensive computational workloads, the infrastructure can maintain the low-latency requirements necessary for precision manufacturing and grid stability, effectively bridging the gap between high-performance operations and rigorous modern cybersecurity standards.
Intelligence at the Edge: The Synergy of DPUs and AI Factories
Effective cybersecurity for critical infrastructure requires an immediate response to anomalies, as even a few seconds of delay in a power grid or chemical plant can lead to irreparable physical damage. The deployment of security intelligence at the network edge allows for real-time enforcement of policies directly at the point of data ingestion, rather than relying on distant cloud-based verification. This localized approach utilizes machine learning models optimized for the edge to identify suspicious patterns in industrial traffic, such as unauthorized command sequences or unusual sensor readings. By processing this information locally on accelerated hardware, the system can autonomously intervene to block malicious activity while allowing legitimate traffic to continue unimpeded. This capability is particularly vital for safety-certified systems that cannot afford the jitter or latency associated with traditional software-based security layers, providing a robust shield that operates at the speed of the underlying physical processes.
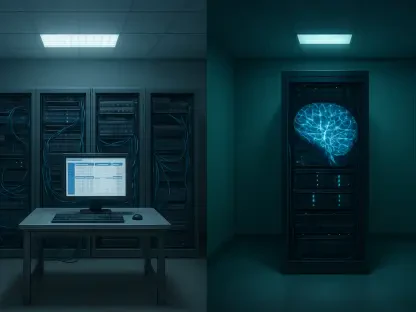
Beyond localized enforcement, the data collected at the network edge is funneled into centralized “AI factories” where massive datasets are analyzed to identify global threat trends and refine security models. These centralized hubs utilize high-performance computing to train advanced neural networks that can predict emerging attack vectors before they are widely exploited in the field. Once a new threat is identified and a countermeasure is developed in the AI factory, the updated security policies can be pushed back out to every DPU across the entire infrastructure in a matter of minutes. This creates a self-reinforcing loop of intelligence where every industrial site benefits from the collective data of the entire network, transforming a fragmented set of utilities into a unified, intelligent defense system. This synergy between edge-level enforcement and centralized AI analysis ensures that the security posture of global infrastructure remains dynamic and capable of evolving as quickly as the threats it is designed to mitigate.
Strategic Ecosystems: Implementing Agentless Zero Trust at Scale
The practical implementation of modern security frameworks like zero trust is often hindered by the inability to install traditional security agents on sensitive industrial equipment or legacy hardware. To overcome this hurdle, NVIDIA has collaborated with partners like Forescout and Akamai to deliver agentless security solutions that operate at the network infrastructure level. By utilizing the BlueField DPU to perform asset discovery and traffic classification, these platforms can gain complete visibility into the network without requiring any modifications to the underlying industrial devices. This allows organizations to implement granular micro-segmentation, effectively compartmentalizing different sections of a factory or utility to prevent the lateral movement of threats. If one segment is compromised, the breach is contained by the hardware-enforced boundaries, ensuring that critical safety systems remain isolated and operational. This method provides a non-intrusive way to modernize the security of decades-old systems while adhering to the strictest compliance standards.
High-speed industrial automation requires a specialized approach where security monitoring must not interfere with the extreme precision and uptime of the production line. Through deep integrations with Siemens and Palo Alto Networks, NVIDIA’s platform enables deep visibility into industrial traffic via specialized AI runtime security models. For instance, the integration within the Siemens Industrial Automation DataCenter allows for continuous monitoring of control traffic at the infrastructure level, detecting subtle deviations that might indicate a cyberattack or a pending mechanical failure. By combining hardware acceleration with advanced threat prevention, these systems provide a comprehensive view of the operational environment that was previously unattainable. This visibility is crucial for maintaining operational excellence, as it allows operators to distinguish between benign technical glitches and malicious intrusions. The result is a unified security architecture that protects both the digital and physical components of modern industrial enterprises without sacrificing throughput.
The Energy-AI Nexus: Securing the Foundations of Modern Power
The security of the energy sector is increasingly dependent on managing complex supply chains and securing access for a wide range of third-party vendors and maintenance technicians. Xage Security has addressed this challenge by deploying its identity-based security platform on the BlueField DPU, creating a decentralized architecture that manages access rights at the edge of the power grid. This system ensures that only verified users and devices can interact with critical energy assets, effectively eliminating the risk of unauthorized access through stolen credentials or compromised vendor accounts. In the context of the modern grid, where distributed energy resources like solar farms and battery storage are becoming more common, this identity-based approach is vital for maintaining resilience. By enforcing security policies at the point of interaction, energy providers can manage a vast array of connected devices without compromising the stability of the overall network, ensuring that the transition to sustainable energy is supported by a robust security framework.
There is a profound interdependence between the energy systems of the world and the AI factories that drive modern technological advancement, as the data centers powering these AI models require massive amounts of reliable electricity. Securing the energy infrastructure is, therefore, a prerequisite for securing the digital future; if the power grid is vulnerable, the AI systems it supports are also at risk. This realization has led to a strategic focus on protecting the physical energy assets that fuel the digital economy. By applying the same AI-driven security models to the power grid that are used to protect high-end data centers, the industry creates a self-reinforcing loop of stability. This approach ensures that the “fuel” for modern intelligence is protected with the same level of rigor as the intelligence itself. As the global demand for compute continues to rise from 2026 to 2028, the resilience of the energy-AI nexus will become the defining factor in the success of the ongoing digital transformation, making integrated hardware security a non-negotiable requirement for industrial operators.
Defining the Future of Industrial Resilience
The protection of critical infrastructure transitioned toward a model of embedded intelligence where security was no longer treated as an external layer but as an intrinsic part of the network fabric. Organizations shifted their focus from peripheral defense to hardware-enforced zero trust, utilizing specialized processors to isolate security logic from operational functions. This movement enabled the modernization of legacy systems that were previously considered impossible to secure, providing a blueprint for the gradual transformation of global utilities. By prioritizing agentless discovery and real-time edge enforcement, industrial operators successfully mitigated the risks associated with IT/OT convergence while maintaining peak operational performance. The industry effectively moved away from reactive patching and toward a predictive, AI-driven posture that could adapt to the speed of emerging threats. These advancements proved that performance and security could coexist in the most demanding physical environments.
Moving forward, stakeholders in the industrial sector should prioritize the adoption of hardware-accelerated security platforms to ensure long-term resilience against increasingly autonomous cyber threats. The implementation of DPUs as a security anchor provided a scalable way to enforce complex policies without introducing operational bottlenecks. Organizations were encouraged to deepen their partnerships with technology providers to create a unified ecosystem that shares threat intelligence across the entire infrastructure. Future considerations must include the continuous refinement of AI models to stay ahead of sophisticated adversaries who also utilize machine learning for offensive operations. By maintaining a commitment to silicon-level security and distributed intelligence, the global community can safeguard the essential services that form the backbone of modern civilization. The shift toward integrated defense ensured that the physical world remained resilient and ready for the next phase of the digital era.