The rhythmic hum of a synchronized assembly line often masks the silent digital vulnerabilities that have recently transformed global manufacturing into the primary target for sophisticated extortion syndicates. In the current climate of 2026, the sector is navigating a profound shift in its risk profile, moving from being an incidental victim to the focal point of organized cybercrime. This change is driven by a perfect storm of aging infrastructure and the rapid adoption of internet-connected technologies that were never designed for the modern threat landscape. Unlike the financial or healthcare sectors, which have spent decades hardening their digital perimeters, many manufacturing entities are just now realizing that their operational continuity is tethered to fragile systems. The stakes have never been higher, as the goal of attackers has moved beyond simple data theft to the total paralysis of physical production. This evolution marks a new era where a single breach can stop global supply chains in their tracks, forcing companies to reconsider their entire approach to industrial security.
The Strategic Exploitation of Industrial Vulnerabilities
Operational Pressures: The Cost of Silence
Modern threat actors have refined their methodologies by focusing specifically on the “downtime-to-dollar” ratio, which measures the immediate financial impact of a production halt. Manufacturers are uniquely sensitive to time because their revenue is tied to the physical output of goods that cannot be replicated or recovered once a shift is lost. When a ransomware strain encrypts the servers managing a shop floor, the ripple effect is felt instantly across the entire enterprise. Attackers recognize that every hour of silence from the machinery translates into massive losses, which provides them with immense leverage during ransom negotiations. This pressure often forces companies to consider paying high demands simply to resume operations before the financial damage becomes irreparable. Furthermore, the specialized nature of industrial equipment means that standard IT recovery protocols are often insufficient to restore the complex calibrations required for precision manufacturing.
Beyond the immediate loss of production, manufacturers are frequently bound by rigid contractual obligations that include severe penalties for missed delivery windows. A cyberattack that paralyzes a facility does not just harm the targeted company; it creates a cascading failure throughout the global supply chain, affecting distributors, retailers, and end-users. This interconnectedness is a primary reason why manufacturing has become such a lucrative target in 2026. Threat actors often research these supply chain relationships to identify the most critical nodes where a single disruption will cause the most chaos. By targeting companies that are essential to the operations of larger conglomerates, attackers ensure that the pressure to settle is applied from both the internal board of directors and external business partners. This environment of high-stakes dependency makes the industry an ideal victim for industrialized extortion where the cost of the ransom is often weighed against the catastrophic cost of a long-term breach.
Legacy Systems: The Vulnerable Foundation
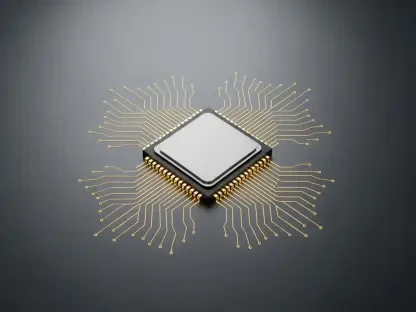
A significant portion of the current threat landscape stems from a historical reliance on legacy industrial hardware that was originally designed to operate in total isolation. These aging Programmable Logic Controllers and Human-Machine Interfaces were built for durability rather than digital security, meaning they lack even the most basic modern protections such as encrypted communications or multi-factor authentication. As these systems are integrated into modern data-tracking platforms to facilitate the efficiency of Industry 4.0, they create permanent “blind spots” that are nearly impossible to secure. Security teams often find themselves in a difficult position where they cannot patch these critical assets because the software updates might cause the hardware to fail, leading to unplanned downtime. This technical debt has left a wide door open for attackers who can easily exploit well-known vulnerabilities that have existed for decades but remain unaddressed on the factory floor.
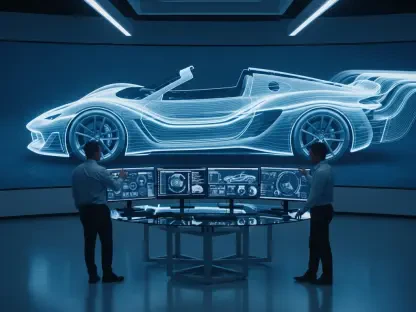
The integration of these legacy assets into internet-facing networks has effectively erased the traditional corporate defense perimeter. When a piece of machinery from the late twentieth century is connected to a cloud-based analytics engine, it becomes an entry point for lateral movement within the network. Attackers utilize specialized scanning tools to identify these unprotected devices, using them as staging grounds to launch further attacks against the more secure parts of the corporate infrastructure. This creates a paradox where the pursuit of modern efficiency through the Industrial Internet of Things actually decreases the overall resilience of the facility. Without a comprehensive strategy to encapsulate or replace these vulnerable systems, manufacturers remain exposed to specialized malware designed to disrupt industrial processes. The inability to monitor these legacy components in real-time means that a breach can go undetected for weeks, allowing attackers to establish deep persistence before they finally trigger the ransomware.
Evolutionary Shifts in the Ransomware Ecosystem
Industrialized Cybercrime: The RaaS Model
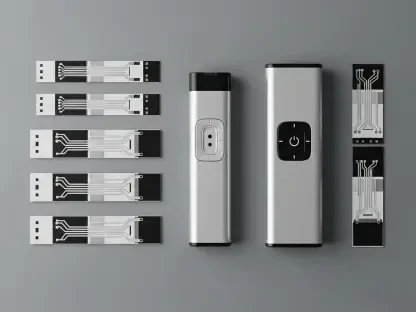
By 2026, the landscape of digital extortion has been redefined by the maturity of Ransomware-as-a-Service models, which provide sophisticated attack tools to a wide range of criminals. This modular approach allows threat groups to purchase high-quality encryption software and access to compromised networks on the dark web, significantly lowering the barrier to entry for attacking complex industrial environments. These kits are now frequently enhanced by artificial intelligence, which automates the initial stages of a breach, such as identifying network misconfigurations or tailoring phishing emails to specific employees. As a result, the volume of active threat groups has surged, leading to a more crowded and dangerous environment for manufacturing IT departments. These attackers are no longer just opportunistic hackers; they are part of a professionalized ecosystem that operates with the efficiency of a legitimate corporation, complete with technical support and negotiation specialists.
The use of AI-assisted reconnaissance has drastically shortened the “dwell time” between an initial entry and the full-scale deployment of ransomware. In previous years, an attacker might spend weeks manually mapping a network, but modern automated scripts can now identify critical assets and escalate privileges in a matter of hours. This speed leaves defensive teams with a very narrow window to detect and neutralize a threat before the production environment is compromised. Furthermore, these industrialized operations are capable of launching simultaneous attacks against multiple targets, stretching the resources of incident response firms. The automation of the attack lifecycle means that manufacturers must move toward automated defensive measures that can respond at machine speed. Relying on human intervention alone is no longer a viable strategy when the adversary is utilizing high-speed algorithms to navigate the network and locate the most sensitive industrial control systems for maximum impact.
Defensive Sabotage: Neutralizing Recovery
A disturbing trend that has solidified in 2026 is the deliberate targeting of a company’s recovery infrastructure long before any encryption takes place. Modern ransomware groups understand that if a victim can simply restore from a backup, the leverage for a ransom payment is lost. Consequently, the first phase of a sophisticated breach now involves the silent identification and destruction of on-domain backup appliances, cloud snapshot repositories, and mirrored storage arrays. By systematically deleting these safety nets, attackers ensure that the only way to recover production data is to purchase the decryption key. This shift from simple encryption to preemptive sabotage has fundamentally changed the nature of incident response. It turns a manageable technical failure into a forced financial decision where the survival of the business is at stake. Many manufacturers have discovered too late that their supposedly secure backups were wiped clean days before the actual ransomware was detonated.
This strategy of neutralizing defenses extends to the targeting of specialized industrial configurations that are often overlooked by general IT security. Attackers now prioritize the theft or destruction of Programmable Logic Controller firmware images and CNC machine calibrations, which are essential for restarting a production line. Even if a company manages to recover its office files, it cannot resume manufacturing without these specific industrial assets. This specialized targeting reflects a deep understanding of the manufacturing process, suggesting that ransomware groups are employing experts with industrial engineering backgrounds to refine their attack vectors. The result is a highly effective form of digital “scorched earth” where the victim is left with no alternative but to negotiate. This evolution highlights the necessity of maintaining truly offline or “air-gapped” backups that are physically disconnected from the main network, as any data reachable through a compromised administrative account is now considered a primary target for destruction.
Strategic Resilience for Production Continuity
Network Segmentation: Creating Digital Barriers
To survive the escalating threats of the current year, the manufacturing sector prioritized the implementation of rigorous technical segmentation between corporate and production environments. This strategy moved away from the “flat” network architectures of the past, where a single compromised credential could grant an attacker access to both the front-office email server and the shop-floor controllers. By creating isolated zones and using industrial firewalls to inspect all traffic moving between the IT and OT domains, companies successfully contained breaches before they reached the assembly line. This approach recognized that while connectivity is essential for data analytics, it must not come at the cost of operational security. Enforced segmentation became the primary defense against lateral movement, ensuring that a phishing attack on an accounting laptop would not lead to a total shutdown of the physical facility. This technical barrier provided the necessary friction to slow down attackers and give security teams the time needed to respond.
In addition to physical and logical segmentation, manufacturers adopted stricter governance over the remote access tools used by third-party maintenance vendors. Historically, these permanent “always-on” connections were a major source of vulnerability, as they bypassed many internal security controls. The transition to session-based access, which required multi-factor authentication and was limited to specific time windows, drastically reduced the available attack surface. Every remote session was monitored and recorded, allowing for immediate termination if any suspicious activity was detected. This shift in management ensured that the convenience of remote troubleshooting did not provide a persistent gateway for cybercriminals. Furthermore, the use of identity-defined perimeters allowed companies to grant access based on the specific role of the user, rather than providing broad network visibility. These governance measures were essential in closing the gaps that had previously allowed attackers to pivot from legitimate maintenance channels into sensitive industrial control systems.
Immutable Recovery: Securing the Final Line of Defense
The final evolution in industrial defense involved the widespread adoption of “immutable” storage solutions, which ensured that data could not be altered or deleted even by those with administrative privileges. This technology provided a genuine safety net against the trend of defensive sabotage, as attackers were unable to wipe the backups needed for recovery. Manufacturers also expanded their disaster recovery plans to include the specialized firmware and configuration files required for industrial machinery, treating them with the same level of importance as financial records. By maintaining these assets in an offline or highly protected state, companies guaranteed that they could rebuild their production environments from scratch if necessary. This shift in perspective focused on the total restoration of the manufacturing process rather than just the recovery of office data. It was this focus on the physical requirements of the factory floor that ultimately allowed the industry to withstand the peak of the ransomware crisis.
The move toward resilient recovery was accompanied by a shift toward proactive security-by-design, where cybersecurity was integrated into the lifecycle of every new piece of equipment. Manufacturers began demanding higher security standards from their suppliers, ensuring that new controllers and sensors were equipped with robust encryption and authenticated boot sequences. This collective effort helped to slowly flush out the legacy vulnerabilities that had plagued the industry for years. By treating digital security as a fundamental component of physical production, the sector successfully navigated the challenges of 2026. The lesson learned was that resilience is not a one-time investment but a continuous process of adaptation and vigilance. Companies that prioritized the protection of their core industrial assets were the ones that maintained continuity and protected their brand reputation in an increasingly hostile digital environment. This comprehensive approach to defense provided the foundation for a more secure and stable future for global manufacturing operations.