The rapid transition toward fully autonomous industrial ecosystems has created a landscape where the microsecond is the most critical unit of operational measurement. In these sophisticated environments, where robotic arms perform high-speed assembly and logistics platforms coordinate movement across vast floor spaces, even a fractional deviation in synchronized time can trigger a chain reaction of mechanical failures. While traditional cybersecurity measures have historically prioritized the protection of data integrity and the prevention of unauthorized network access, a more insidious threat has emerged that targets the very heartbeat of the factory. These temporal disruptions do not seek to steal proprietary information or encrypt files for ransom; instead, they manipulate the delicate timing protocols that govern the physical interactions of machinery. This shift in adversarial strategy represents a fundamental challenge for the modern industrial sector, as the subtle nature of these attacks allows them to bypass conventional security systems designed to detect more overt forms of digital interference.
Vulnerabilities in Deterministic Industrial Networking Protocols
The foundation of modern industrial communication relies heavily on specialized protocols like Time-Triggered Ethernet, which ensures that safety-critical data reaches its destination at precise intervals. This deterministic approach is essential for high-stakes environments such as aerospace manufacturing and pharmaceutical production, where the sequence of operations must be followed with zero tolerance for error. However, recent research suggests that the inherent trust these systems place in time synchronization is exactly what makes them vulnerable to sophisticated spoofing and man-in-the-middle attacks. By injecting minute amounts of latency or subtly altering time-stamped messages, a malicious actor can desynchronize a local network without triggering the alarms associated with data loss or unauthorized logins. This level of precision allows an attacker to remain hidden within the background noise of standard network traffic, making the detection of such interference nearly impossible for legacy monitoring tools that lack temporal awareness.
Building on the technical nuances of these vulnerabilities, the complexity of Industry 4.0 integration often complicates the task of securing every temporal node. Many factories now operate on a hybrid infrastructure where newer, time-sensitive networking components must communicate with older industrial control systems that were never designed to withstand targeted timing manipulation. This creates a fragmented security perimeter where an attacker can exploit the weakest link in the synchronization chain to propagate errors throughout the entire assembly line. Because these attacks focus on the delivery timing rather than the payload of the message, they effectively circumvent encryption and standard firewalls. The result is a specialized form of digital sabotage that can be tuned to cause either immediate mechanical failure or long-term, cumulative degradation of equipment. As these stealthy techniques become more refined, the industry must recognize that the integrity of a time signal is just as vital as the confidentiality of the data it carries.
Operational Consequences and the Future of Temporal Security
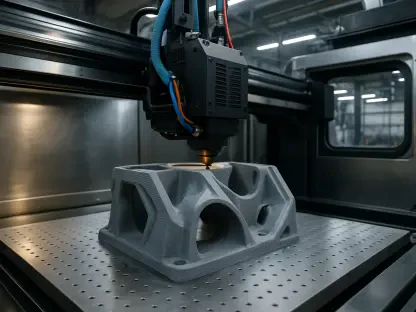
The physical repercussions of a successful time-based attack can be devastating for a manufacturer, leading to irreversible product defects or the complete shutdown of critical safety systems. In a high-precision environment, a delay of just a few milliseconds in a conveyor belt’s logic can cause robotic components to collide or miss their mark, resulting in thousands of dollars in wasted materials and equipment damage. Beyond the immediate financial loss, these incidents pose a significant risk to human workers who rely on automated safety barriers and emergency stop protocols that are also governed by the same synchronized clocks. When the temporal logic of a factory is compromised, the predictable behavior of the machinery vanishes, creating an unpredictable and hazardous workspace. This scenario forces a reevaluation of how safety is defined in the digital age, moving beyond mechanical guards to include the verification of the invisible signals that synchronize every movement on the production floor.
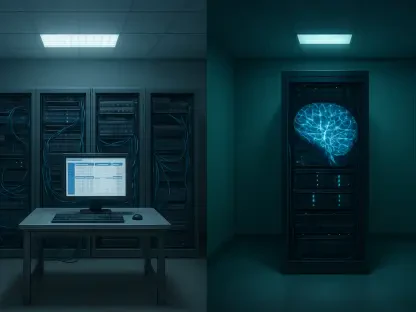
To mitigate these emerging risks, industrial leaders must move toward a more resilient architecture that incorporates multi-layered temporal verification and anomaly detection specifically tuned for timing deviations. Relying on a single source of truth for time synchronization is no longer a viable strategy in a landscape where spoofing techniques have become so advanced. Instead, implementing redundant timing sources, such as combining localized atomic clocks with secure satellite-based signals, can provide a cross-reference point to identify discrepancies before they manifest as physical errors. Furthermore, the integration of artificial intelligence into network monitoring can help identify subtle patterns of jitter or latency that deviate from the established baseline, providing an early warning system for stealthy intrusions. Moving forward, the manufacturing sector must treat temporal integrity as a core pillar of its broader cybersecurity strategy, ensuring that the clocks governing our most critical infrastructures remain accurate and unassailable in the face of evolving digital threats.
The investigation into these vulnerabilities concluded that the lack of rigorous authentication within time-triggering mechanisms allowed for the successful execution of stealthy interference. Researchers determined that traditional defensive perimeters failed to identify the manipulation because the structural format of the communication remained within expected parameters. This gap in security was addressed by proposing a decentralized synchronization model that reduced reliance on a single master clock. The study verified that implementing these more robust verification protocols significantly decreased the likelihood of a successful temporal breach. Ultimately, the industry shifted toward adopting more resilient standards that treated timing data with the same level of scrutiny as financial or intellectual property. By integrating these lessons into current infrastructure, organizations managed to bolster the reliability of autonomous operations and protect the long-term viability of the smart factory model.