Tankers threaded the narrows as escorts bristled with sensors, yet a $30,000 drone still promised to upend a billion-dollar convoy and the global markets that depend on it. The wager at the center of current debate is simple but unforgiving: whether a 1980s-style U.S. convoy model can credibly protect commerce through the Strait of Hormuz when cheap, agile, and networked threats tilt the economics toward disruption. The strait still moves roughly one-fifth of seaborne oil and substantial LNG, so a single high-profile strike can spike premiums, reroute fleets, and jolt prices faster than policy can respond.
This trend matters because the offense–defense cost curve has bent further in favor of the attacker. Iran’s blend of swarming fast craft, one-way attack UAVs, short-range missiles, modern mines, and cyber-enabled targeting compresses warning time and complicates attribution. Moreover, political fragmentation—among allies and within the mission set—blurs the signaling that once anchored coalition escort efforts, challenging the assumption that more warships equal more confidence.
Then and Now: Comparing the Tanker War to Today’s Asymmetric Battlespace
Operation Earnest Will offered a template built on narrow goals: reflag select tankers, keep oil moving, and deter strikes on escorted hulls. It endured serious shocks—the Bridgeton and USS Samuel B. Roberts mine strikes, the USS Stark missile hit, and the tragedy of Iran Air Flight 655—yet achieved its limited purpose under Cold War constraints that bounded escalation and clarified messages to allies and adversaries.
Today’s battlespace is broader, faster, and harder to police. Since recent flare-ups, incident profiles shifted from mostly mines and anti-ship missiles to a mixed menu of limpet mines, fast-attack craft, drones, and cyber-enabled surveillance cited by IISS, CSIS, and industry reporting. The visible result is a market that reacts within hours: war risk premiums and deviation costs jump after even isolated seizures, while shipowners discount partial or flag-limited protection as insufficient to anchor schedules or credit lines.
What the Numbers Say: Shipping Flow, Threat Incidents, and Risk Pricing
Throughput remains the immovable baseline. U.S. EIA and IEA estimate Hormuz carries close to one-fifth of global seaborne oil plus significant LNG volumes, which means any escort regime that fails publicly risks immediate financial contagion. Markets price not just damage but doubt; confidence is an asset class here, and one easily marked down.
Cost asymmetry magnifies this fragility. SIPRI and RAND analyses underline that cheap UAVs and USVs can force expensive defensive shots, draining magazines and budgets. Brokers echo the signal: Lloyd’s Market Association designations and advisories push premiums higher at the first hint of escalation, while recent NATO and EU statements suggest allied appetite for open-ended, broad-scope escorts faded without tight objectives and burden-sharing.
Historical Template vs. Current Reality: Case Studies and Operational Lessons
The 1980s showed that escorts can work if the mission is narrow and signaling is clear. However, they also revealed escalation risk, from mine strikes that nearly sank a frigate to misidentification that ended in catastrophe. The lesson endures: tactical success can coexist with strategic fragility when the political frame is thin.
Contemporary cases underscore new stresses. Iranian boardings and small-boat swarms pierced assumptions about deterrence under nominal ceasefires. In the Red Sea, intense air and surface defense against Houthi salvos delivered the Navy’s hardest surface combat in decades, highlighting magazine depth, ISR fusion, and counter-UAS as gating factors. European hesitation to expand Hormuz escorts absent de-escalation, and shipper skepticism that U.S.-led convoys reduce risk when the U.S. is a principal adversary, further constrain credibility.
What Experts Say: Objectives, Constraints, and Credibility
Analysts such as Torbjorn Soltvedt describe a widened asymmetric edge: diffusion of drones, smart mines, and FAC/FIAC swarms stretched defenses beyond 1980s complexity. Former diplomat and naval officer Tom Duffy points to a strategy clarity gap—the “kaleidoscope” of goals from deterrence to regime pressure—making planning, ROE alignment, and alliance-building harder than under Reagan-era focus.
There is tentative consensus on limits. No escort can promise impermeability, and one successful strike can puncture confidence. “Shoot and kill” guidance against hostile small craft may avert proximate danger but cannot substitute for a political framework that constrains Iran’s strike complex. Narrowing concern to select flags erodes the broader freedom-of-navigation message that once rallied partners.
Pathways Ahead: Capabilities, Concepts, and Diplomacy Under Constraint
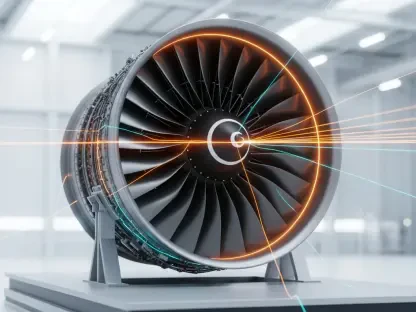
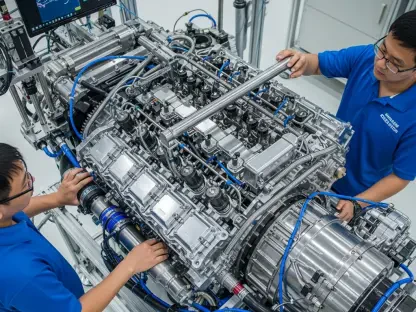
A viable path trends toward conditions-based escorting: time-bound windows, corridor-specific coverage, and explicit thresholds for suspension or surge. Layered defense needs to assume mixed salvos—distributed sensors, AI cueing, rapid-reload interceptors, EW, and agile unmanned mine countermeasures working as a single architecture rather than a stack of bolt-ons.
Technology will not rescue poor strategy, but it can compress response cycles. Proliferating one-way UAVs and smarter mines raise denial potential; defense leans on passive sensors, resilient comms, and rigorous magazine management. Commercial operators increasingly add citadels, RF monitoring, soft-kill kits, and tighter AIS discipline, while data-sharing must balance transparency with OPSEC to avoid handing targets a roadmap.
Diplomacy remains the hinge. Hotlines, incident-at-sea protocols, and tacit limits on drone and missile employment near shipping lanes can lower the temperature. Conditional coalitions—with precise scopes, shared ROE, and cost-sharing—earn broader buy-in. Economic levers, from insurance backstops to guaranteed routing windows, can stabilize behavior when tempers and premiums rise.
Bottom Line and Next Steps
The trend pointed toward replicating the form of 1980s escorts but not their function under current conditions. Strategic clarity proved the non-negotiable first step: define whether protection covered all commercial traffic or only select flags and cargoes, and fix time limits. Means had to match ends—ISR density, replenishment plans, and legal authorities—while coalition credibility depended on unified messaging and burden-sharing. Most of all, escorts worked only when paired with diplomacy that limited Iran’s capacity or incentives to strike.
Actionable next moves sat in plain sight. Policymakers set narrow, transparent missions and resisted overpromising; allies and industry conditioned participation on clear thresholds for pause or surge; planners invested in counter-UAS/USV, unmanned MCM, resilient comms, and magazine depth. Taken together, these choices shifted the balance from brittle symbolism to durable assurance, even as the offense–defense ledger continued to favor disruption.