The steady rhythmic hum of precision machinery has returned to Foxconn’s North American assembly lines, but the silence following a massive digital breach remains deafening for the world’s most powerful technology companies. While the physical gears are turning once again, a catastrophic data heist has left a trail of exposure that stretches far beyond the factory walls in Wisconsin and Mexico. The recent infiltration by the Nitrogen ransomware group resulted in the extraction of 11 million files—a staggering 8 terabytes of data—representing what can only be described as the collective “digital DNA” of industry titans like Apple, Nvidia, Intel, and Google.
This was not a rudimentary attempt to freeze production for a quick payout; it was a surgical extraction of the proprietary blueprints that govern the modern digital world. For years, the manufacturing sector has been a prime target for extortionists, yet this specific incident elevates the stakes to a level of existential risk. When the schematics for next-generation servers and consumer electronics are siphoned off by the terabyte, the conversation shifts from temporary business interruption to the permanent compromise of global intellectual property.
The 8-Terabyte Heist That Stripped the Tech Industry Bare
The scale of the Nitrogen breach is difficult to overstate, effectively laying bare the internal secrets of the global tech supply chain. By infiltrating Foxconn’s infrastructure, attackers gained access to a trove of documents that were never intended for eyes outside of highly secured clean rooms. This data represents the lifeblood of innovation, containing the precise details that allow companies to maintain a competitive edge in a hyper-aggressive market.
Furthermore, the nature of the stolen material suggests a deep understanding of what makes a modern tech giant vulnerable. This was not a random grab of administrative spreadsheets or HR records; the hackers targeted the very blueprints that define how hardware is built and how it functions. With 8 terabytes of information now circulating in the shadows, the industry faces a reality where the “secret sauce” of its most successful products has been transformed into a public commodity for those with the means to exploit it.
Understanding the Shift from Operational Downtime to Intellectual Property Warfare
Historically, ransomware attacks on manufacturers aimed to freeze the factory floor, using the high cost of idle machinery as leverage for immediate extortion. However, the Foxconn-Nitrogen incident signals a definitive departure from this trend, prioritizing long-term architectural risk over short-term operational disruption. For a global leader like Foxconn, the concern is no longer just about meeting a shipping deadline in the current quarter, but the reality that the structural integrity of future hardware is now compromised.
This strategic shift forces a reckoning for the entire supply chain, as the security of a single vendor is now inextricably linked to the survival of its high-profile clients’ intellectual property. When a manufacturer falls, the damage is no longer contained within its own balance sheet. Instead, it ripples outward, potentially devaluing years of research and development for the brands that rely on that manufacturer’s discretion. This evolution in cyber warfare means that the defense of a factory is now the defense of the brand itself.
Deconstructing the Nitrogen Incident and the Loss of Proprietary Hardware Specs
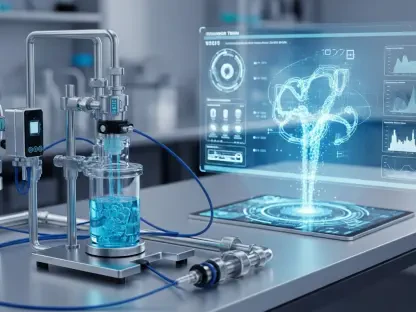
The breach target was comprehensive, moving far beyond typical corporate data into the realm of deep engineering and hardware architecture. Stolen assets include intricate motherboard diagrams, Printed Circuit Board layouts, and I3C/I2C topology specifications—the literal maps of how data flows through a device. Moreover, the theft of specialized thermal and liquid leakage sensor designs puts the physical integrity of high-performance data centers at risk, as these components are vital for maintaining the stability of modern AI infrastructure.
The threat actor, a group known as Nitrogen, represents a new breed of extortionist that has adapted to the technical limitations of its own tools. Due to flaws in their encryption software that often corrupt data beyond repair, they have transitioned toward a “pure data-theft” model. In this scenario, the primary threat is the public leak of these highly sensitive blueprints rather than the locking of systems. This approach makes the attack far more dangerous, as the damage caused by a leak cannot be undone by a simple decryption key.
Why Industry Experts View the Leak as a Generational Threat to Hardware Integrity
Security analysts have reached a consensus that the fallout from this breach will persist for years, as the leaked documentation provides a masterclass for both counterfeiters and sophisticated hackers. With access to precise engineering drawings, bad actors can produce “knock-off” hardware that is visually and functionally identical to the original but built with substandard components. This creates a secondary market of dangerous imitations that can undermine consumer trust and cause significant financial damage to the original creators.
Even more concerning is the threat of “living-off-the-land” hardware attacks, where adversaries study the DNA of these devices to identify zero-day firmware vulnerabilities. Because these flaws are baked into the hardware logic, they are nearly impossible to patch via traditional software updates. This effectively turns the world’s most advanced technology into a public liability, as engineers must now assume their internal blueprints are being scrutinized by hostile entities looking for the smallest crack in the foundation.
Strategic Frameworks for Securing the Future of Global Manufacturing
To mitigate the risks posed by such a massive exposure, tech giants and their manufacturing partners must adopt a radical shift in how they perceive product security. This begins with rigorous, recurring firmware auditing and the implementation of “zero-trust” principles at the hardware level. Systems must be designed with the assumption that every interface is potentially compromised, requiring cryptographic proof for every internal communication. Hardware-facing interfaces should be built to remain secure even if the underlying blueprints are common knowledge.
Companies must also diversify their security protocols across the entire supply chain to ensure that a breach at one facility does not grant a roadmap to an entire global infrastructure. Moving forward, the industry worked toward a model where hardware resilience was no longer a hidden secret but a measurable standard. Engineers prioritized cryptographic resilience that could withstand the transparency of a leaked schematic. By treating hardware security as a dynamic, evolving discipline rather than a static wall, the manufacturing sector began to build a future where data-theft incidents could no longer dismantle the integrity of global innovation.